A Technological Fix: The Adoption of Chinese Public Security Systems
The paper examines the proliferation of Chinese surveillance tools. It seeks to point out how supply and demand factors result in the proliferation of public security platforms. With special attention to local factors, the paper shows how local procurement is critically driven by public security ambitions and justified as a means towards development in African countries. An inquiry into the proliferation of Chinese public security systems in Africa offers a vantage point to consider how Beijing’s growing involvement and corporate activities are meditated by local factors.
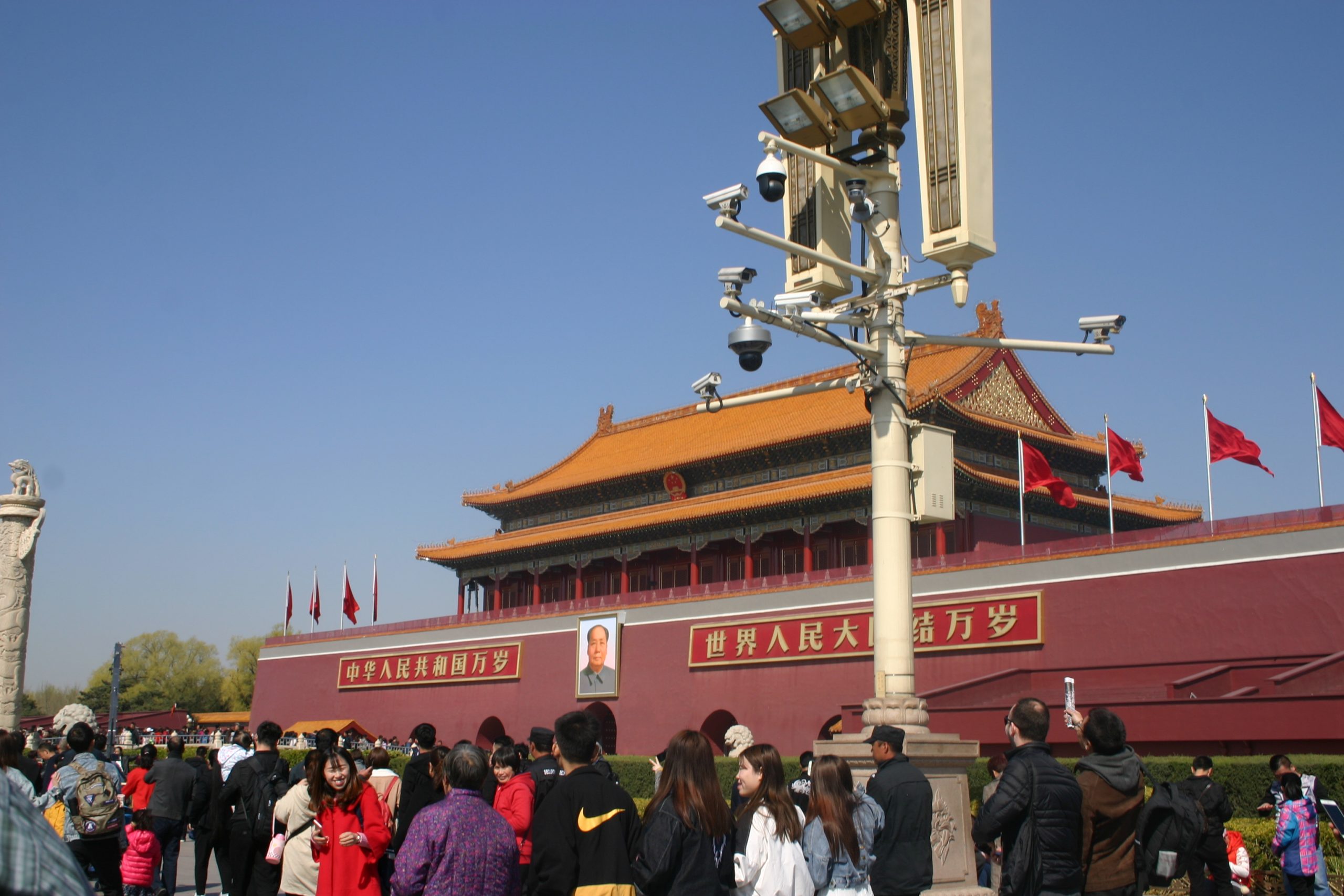
The Global Spread of China’s Surveillance Tools
In Uganda, the Kampala police procured 6 million worth of AI public security platforms from Huawei, purportedly to ameliorate the city’s growing incidences of violent crime. Public security systems are part of state-led initiatives to resolve digital infrastructure gaps. On the other hand, they are also enlisted to address traditional challenges to public safety. While ostensibly permissible motivations drive Chinese surveillance technology adoption, its application comes without accountability mechanisms or public involvement. Indeed, this lacuna between the promotion of AI surveillance technologies and regulatory measures inspires perturbation over the atrophy of liberties. This concern appears to be credible, as local civil rights organizations and opposition leaders in Uganda contend that adopting these systems results in extralegal surveillance and interception of the communications of opposition leaders to the Museveni administration.
Uganda is not an outlier. In Zimbabwe, without robust accountability measures, the state partnered with Cloudwalk, a Guangdong-based AI startup, to adopt facial recognition capability to support law enforcement and digital forensic operations. China’s willingness to work with authoritarian regimes like Zimbabwe, which have a history of unwarranted surveillance and a record of violating human rights, is problematic, to say the least. Regardless of the intentions behind the use of public security technologies, they undoubtedly scale the state’s capacity to surveil. As such, this concern with surveillance is not exclusive to authoritarian governments: accruing state power, even in democracies like South Africa, can result in unwarranted surveillance practices without the establishment of the needed checks and balances. China’s penchant for supporting African authorities, regardless of their human rights record, renders citizens more vulnerable to the misuse of digital surveillance tools.
China’s surveillance system is confined to its national borders, but the enterprises that make its intrusive practices possible are now selling their public security tools to an international customer base. Beijing helps promote surveillance technology abroad through training programs, diplomatic exchanges, and law enforcement cooperation. These endeavors enable the dissemination of public security systems, but also support the party-state’s aims to influence international norms and practices. In this light, about 22 African countries have contracted Chinese firms to help engender public security systems. Around half of Africa’s countries do not have data protection laws. If they do, they often lack lucid enforcement mechanisms and technical means in place to promote privacy. Given these gaps, observers contend that Beijing’s active push to promote the adoption of surveillance tools in the global south is a critical vector that is driving the rise of authoritarianism. While this line of inquiry crucially underscores how Chinese authorities may leverage African demand factors to promote their own geopolitical interests, this framework overlooks local agency in the procurement and adoption of digital surveillance technologies. More saliently, this argument also presumes a level of coordination between private firms and Beijing as a strategy to promote its tools and normative values.
African Adoption of Surveillance Tools
The adoption of public security platforms in Kenya is in part a result of Huawei’s Safe Cities projects. Briefly, the smart city is a computational model of urban planning that promises to augment efficacy and economic development by best utilizing digital infrastructure. Like elsewhere in Africa, smart city initiatives arrive on the backs of Chinese aid and development assistance.
Beijing’s approach to African countries has never been coercive but always remunerative. Beijing bases their approach on offering aid and incentives to promote diplomatic relations, and with private and state support, Kenya was able to connect 1,800 high-definition cameras and 200 high-definition traffic surveillance systems across downtown Nairobi. Moreover, a national police command center was founded to offer support to over 9,000 police officers and 195 police stations. Through wireless infrastructure, the cameras send their data to the Integrated Control and Communication Center (IC3) at the National Police Headquarters. The adoption of novel systems seeks to support crime prevention and recovery operations.
The lack of evidence that demonstrates ICT platforms’ capabilities to truncate incidences of crime does not deter the promotion of public security platforms in Kenya. In the case of Nairobi, crime rates have risen in neighborhoods supported by ICT platforms. Adam Lane, Deputy CEO of Government Affairs Huawei Kenya, admits that “a wide variety of factors affect insecurity such as lighting, drug use, unemployment, or inequality, and ultimately preventing crime requires addressing these causes of crime in a very local way.” He continues: “our solution cannot address these, but it can help support some of the causes, and certainly helps with prevention and response to crime.” Due to the silence and dearth of publicly available data about the performance of these novel systems, it is hard to verify the achievements of public security systems. According to Huawei, crime rates in Kenya decreased by 46 percent between 2014 and 2015 in areas supported by their surveillance tools. However, the National Police Service reports show smaller reductions in crime during those years in Nairobi.
Relatedly, no empirical evidence exists from African case studies that convincingly establish China’s coordination and collaboration between its authorities and firms that results in the promotion of surveillance practices in Africa. The lack of attribution does not alleviate perturbation. In fact, I argue, the dearth of evidence regarding coordination intimates the paramount need to further ensure supply chain integrity given the ubiquitous potential to install backdoors in hardware and software products surreptitiously. Nonetheless, despite growing trepidations over democratic backsliding and the real risk of backdoors installed in hardware and software, African authorities continue to procure public security platforms from private Chinese firms. This decision is primarily predicated on the financial reachability of Chinese public security platforms. Most importantly, on the ostensible grounds that the technology can bridge digital infrastructure gaps and improve public safety.
Accountability and Transparency
Without a doubt, digital infrastructure is being deployed in Kenya and across the continent to address social and political challenges. In addition to making ICT more accessible to ordinary Kenyans, there is a demand for security, which is both a response to trepidation surrounding terrorism and crime. The government, with its Chinese partners, has quickly deployed these tools without considering their impact on human rights. For example, facial recognition systems rely on large sums of biometric data, yet it is not clear where the images are obtained or how the Kenyan state is using this image data. Simply put, data collection conducted by the state with the technical support of its partners can impact human rights depending on where and under what conditions they source and use biometric data. The state and its partners can undercut subjects’ rights to remedy if they do not provide the means to know whether their personal data is collected, and they can request removal of their personal data. All this means is that the government’s use of facial recognition systems lacks clarity or accountability. Most importantly, the state and its partners can contribute to human rights risks if they are not intentional and transparent about collecting and managing biometric data.
While Beijing’s ICT engagement in Africa does not demonstrate an intention to promote China’s surveillance practices, it does engender the conditions for doing so. How long Beijing chooses to maintain its no-strings-attached posture is a salient matter, as it has real consequences for African authorities and their digital environments. Another thing, digital platforms mirror the political constellations in which they are embedded in and form novel socio-technical interlinkages that have consequences. Thus far, a limited number of studies have drawn attention to the multiple uses, properties, and applications of these digital devices in local environments. Digital public security platforms are ostensibly used to improve service delivery, enhance law enforcement, and streamline administrative processes. Technologies are conscripted to resolve structural and political challenges. What is lucid is that there is no direct correlation between using digital surveillance tools and reducing crime. Indeed, the presumption that social complexities like crime can be reduced to a technological fix challenges us to consider how technologies are constructed as modalities of social intervention and correction. These modalities, at times, obfuscate the local contingents that maintain crime as a social problem but also add to the fiction of technology as a smoothly functioning instrument that provides a reliable and equitable solution to development challenges.
. . .
Bulelani Jili is a Meta Research Ph.D. Fellow at Harvard University. His research interests include US-China competition, ICT Development, Africa-China relations, Cybersecurity, National Security, Algorithmic Decision-Making, and Privacy Law. He is also a Visiting Fellow at Yale Law School, Cybersecurity Fellow at the Harvard Kennedy School, Fellow at the Atlantic Council, Scholar-in-residence at the Electronic Privacy Information Center, Visiting Fellow at Hong Kong University Law, and Research Associate at Oxford University.
Image Credit: Wikimedia Commons, CC 3.0.